This category contains some of my older pages which still contains some relevant information.
This is the multi-page printable view of this section. Click here to print.
Archive
- Welcome to justinverstijnen.nl v2
- Azure Key Vault
- The MITRE ATTACK Framework
- The Zero Trust-model
- Introduction to the Microsoft Cloud Security Benchmark (MCSB)
- Introduction to the Azure Well-Architected Framework
- Cloud Adoption Framework Introduction (CAF)
- AI-900 My learning journey
Welcome to justinverstijnen.nl v2
Welcome to justinverstijnen.nl v2
Welcome to my completely renewed website. The past month I’ve been busy rebuilding my old Wordpress website to a completely new website based on GitHub Pages. I wanted to enhance this website on the following areas:
- Light/Dark mode
- Better experience on mobile devices
- Uniform pages and posts
- Scalable and future-proof solution
Why this new update?
My old website was great, but with Wordpress and some specific requirements I had, it became obsolete to me. I couldn’t find a great skin other than I already had for the complete lifecycle of it which I still really like. It required me to have around 300 lines of extra CSS to get the website to my likings but still had an inconsistent experience across multiple devices. Also I needed around 28 plugins to make everything work, making it a mess sometimes.
Flight blog
I also wanted to separate my technical career blog from my flight blog, which is also renewed. You can find this here if interested: flightblog.justinverstijnen.nl
On my flight blog, I write about achieving my Private Pilot License (PPL) and the flying lessons themselves which I really find fun to do.
Azure Key Vault
Azure Key Vault is a type of vault used to store sensitive technical information, such as:
- Certificates
- Secrets
- Keys
What sets Azure Key Vault apart from a traditional password manager is that it allows software to integrate with the vault. Instead of hardcoding a secret, the software can retrieve it from the vault. Additionally, it is possible to rotate a secret every month, enabling the application to use a different secret each month.
Practical use cases include:
- Storing BitLocker encryption keys for virtual machines
- Storing Azure Disk Encryption keys
- Storing the secret of an Entra ID app registration
- Storing API keys
How does Azure Key Vault work?
The sensitive information can be retrieved via a unique URL for each entry. This URL is then used in the application code, and the secret is only released if sufficient permissions are granted.
To retrieve information from a Key Vault, a Managed Identity is used. This is considered a best practice since it is linked to a resource.
Access to Azure Key Vault can be managed in two ways:
- Access Policies
- Provides access to a specific category but not individual entries.
- RBAC (Recommended Option)
- Allows access to be granted at the entry level.
A Managed Identity can also be used in languages like PHP. In this case, you first request an access token, which then provides access to the information in the vault.
There is also a Premium option, which ensures that Keys in a Key Vault are stored on a hardware security module (HSM). This allows the use of a higher level of encryption keys and meets certain compliance standards that require this level of security.
End of the page 🎉
You have reached the end of the page. You can navigate through other blog posts as well, share this post on X, LinkedIn and Reddit or return to the blog posts collection page. Thank you for visiting this post.
If you think something is wrong with this post or you want to know more, you can send me a message to one of my social profiles at: https://justinverstijnen.nl/about/
If you find this page and blog very useful and you want to leave a donation, you can use the button below to buy me a beer. Hosting and maintaining a website takes a lot of time and money. Thank you in advance and cheers :)
The terms and conditions apply to this post.
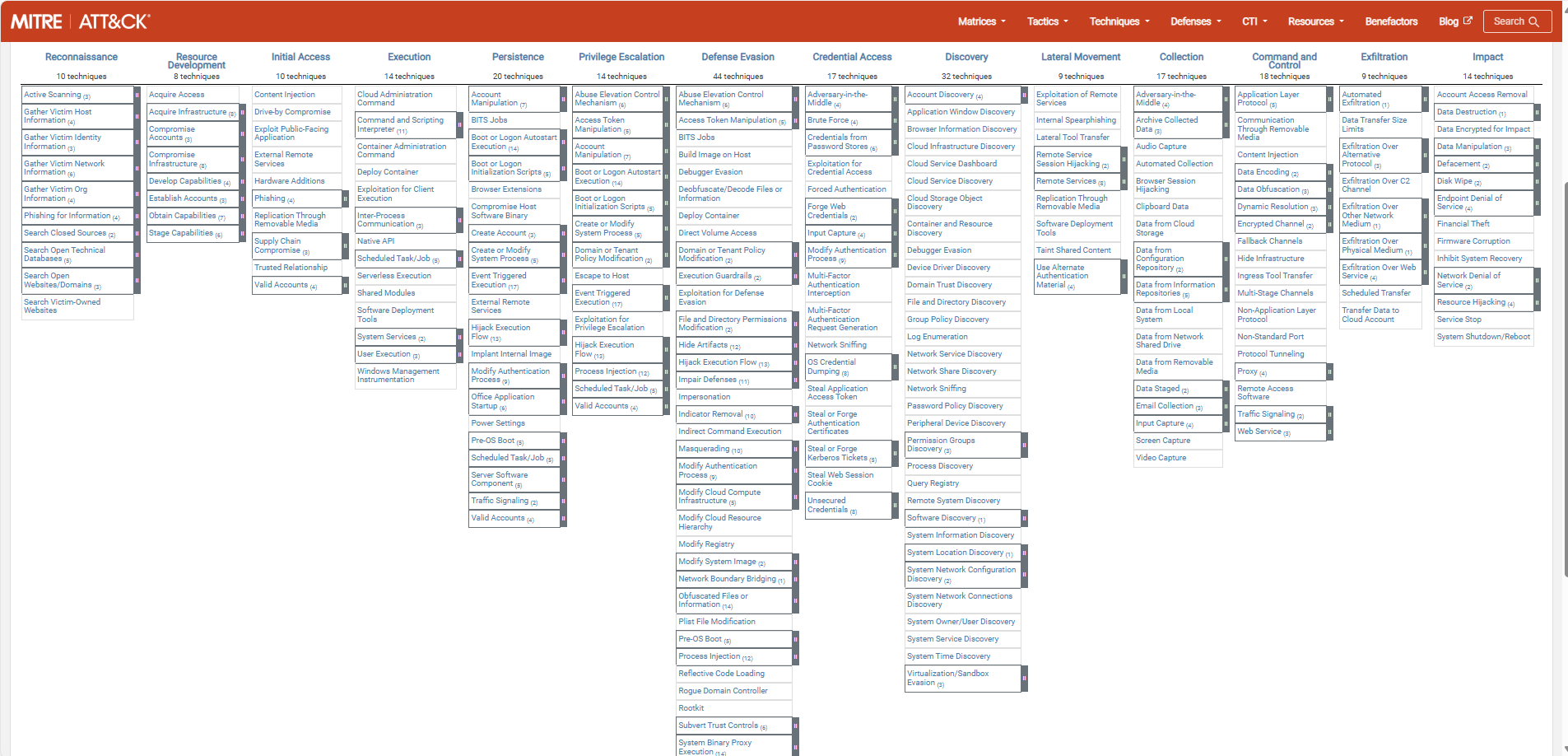
The MITRE ATTACK Framework
The MITRE ATTACK (ATT&CK) Framework is a framework which describes all stages and methods cyberattacks attacks are launched on companies in the last 15 years. The main purpose of the framework is to help Red and Blue security teams to harden their systems and to provide a library of known attacks to help mitigate them.
MITRE is the organization who is in charge of this community-driven framework and is a non-profit organization. ATT&CK stands for:
- Adversary -> Our opponents
- Tactics
- Techniques
- Common Knowledge
The framework itself can help organizations help to secure their environment really good, but keep in mind that the framework is built based on known attacks and techniques. It doesn’t cover new techniques where an organization can be vulnerable to.
The framework itself
The framework can be found on this website: MITRE ATT&CK®
The stages of a cyberattack
Each cybersecurity attack follows multiple or all stages below. Also, i added a summary of that the stage contains:
| Stage | Primary goal |
| Reconnaissance | Gathering information prior to the attack |
| Resource Development | Aquiring the components to perform the attack |
| Initial Access | Initial attempts to get access, the attack starts |
| Execution | Custom-made code (if applicable) will be executed by the adversary |
| Persistence | The attacker wants to keep access to the systems by creating backdoors |
| Privilege Escalation | The attacker tries to get more permissions than he already has |
| Defense Evasion | The attacker wants to avoid detection for a “louder bang” |
| Credential Access | Stealing account names and passwords |
| Discovery | Performing a discovery of the network |
| Lateral Movement | Aquire access to critical systems |
| Collection | Collecting data which often is sensitive/PII* data |
| Command and Control | The attacker has full control over the systems and can install malware |
| Exfiltration | The attacker copies the collected data out of the victims network to his own storage |
| Impact | The attacker destroys your systems and data |
*PII: Personal Identifible Information, like birth names and citizen service numbers
The attack stages are described very consise, but the full explaination can be found on the official website.
Summary
The MITRE ATT&CK framework is a very great framework to get a clear understanding about what techniques and tactices an attacker may use. This is can be a huge improvement by securing your systems by thinking like a attacker.
The best part about the framework are the mitigation steps where you can implement changes to prevent attacks that already happend with a big impact.
End of the page 🎉
You have reached the end of the page. You can navigate through other blog posts as well, share this post on X, LinkedIn and Reddit or return to the blog posts collection page. Thank you for visiting this post.
If you think something is wrong with this post or you want to know more, you can send me a message to one of my social profiles at: https://justinverstijnen.nl/about/
If you find this page and blog very useful and you want to leave a donation, you can use the button below to buy me a beer. Hosting and maintaining a website takes a lot of time and money. Thank you in advance and cheers :)
The terms and conditions apply to this post.
The Zero Trust-model
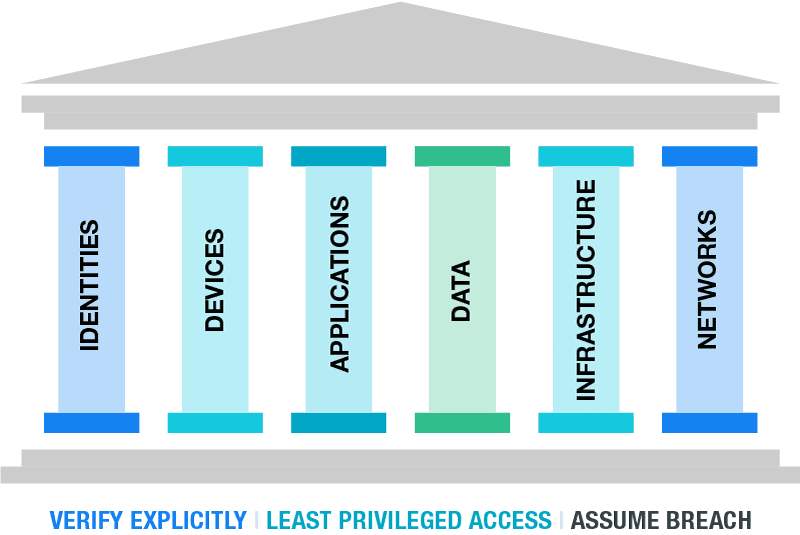
The Zero Trust model is a security model to enhance your security posture by using 3 basic principles, and segmenting aspects of your IT environment into pillars.
The 3 primary principles are:
- Verify Explicitly
- Least privileged access
- Assume Breach
At first, those terms seem very unclear to me. To further clarify the principles, i have added some practice examples to further understand what they mean:
| Principle | Outcomes |
| Verify Explicity | Ensure people are really who they say they are Audit every login attempt from specific users Audit login attempts Block access from non-approved countries |
| Least privileged access | Assign users only the permissions they need, not more Assign only the roles when they need them using PIM Use custom roles when default roles expose too much permissions |
| Assume breach | At every level, think about possible breaches Segment your network Password-based authentication only is too weak |
The model is the best illustrated like this:
Your security posture can be seen as a building. The principles are the foundation, and all aspects in a organization are the pillars.
The fun fact in this model is, that if the foundation and/or one of the pillars are not secured enough, your security posture collapses like a unstable building.
A fun example of this can be a 5 million dollar cybersecurity budget, but users are not using strong authentication to logon and are getting compromised.
Zero Trust vs Traditional approaches
The last 20 years, the network was the primairy pillar. If a malicious user or device doesn’t have access to your network, no breach is possible.
The last 5 years, especially now in the post-COVID19 period, more people tend to work remotely. Also are companies shifting to cloud applications and infrastructure. This makes the pillar of Identity now the primary pillar, because this is the way users connecto to their infrastructure, applications and data. Breaching one of the pillar can give access to all.
The stupid part is, the Identity pillar is the pillar where the most people come along. People make mistakes and that is exactly where attackers are searching for. The path of the least resistance.
How to ramp up Zero Trust
Changes to your infrastructure, especially when talking about Security can take up very much of your time and can get complex very fast. Most companies will disregard the changes and go on, when still using unsecured systems until a great company-devastating breach.
To roll out the most critical Zero trust principles in a short timely manner, you can use the RaMP plan which is a Rapid Modernization plan. This gives you a kickstart, but leaves the more complex and time-consuming changes for the near-future.
To further expand your Zero Trust vision and security posture, a great resource is to use the following 2 references by Microsoft:
Azure Cybersecurity Benchmark: https://learn.microsoft.com/en-us/security/benchmark/azure/overview-v3
- This contains monthly updated benchmark points which you can lay against your organizations operations. These are all best practices from a security standpoint to secure the environment on all aspects and pillars
Azure Cybersecurity Reference Architectures: https://github.com/MicrosoftDocs/security/blob/main/Downloads/mcra-december-2023.pptx?raw=true
- To get some inspiration about how to build your cybersecurity architecture
End of the page 🎉
You have reached the end of the page. You can navigate through other blog posts as well, share this post on X, LinkedIn and Reddit or return to the blog posts collection page. Thank you for visiting this post.
If you think something is wrong with this post or you want to know more, you can send me a message to one of my social profiles at: https://justinverstijnen.nl/about/
If you find this page and blog very useful and you want to leave a donation, you can use the button below to buy me a beer. Hosting and maintaining a website takes a lot of time and money. Thank you in advance and cheers :)
The terms and conditions apply to this post.
Introduction to the Microsoft Cloud Security Benchmark (MCSB)
To have a good overview of how secure your complete IT environment is, Microsoft released the Microsoft Cloud Security Benchmark, which is an collection of high-impact security recommendations you can use to secure your cloud services, even when utilizing a hybrid environment. When using Microsoft Defender for Cloud, this MCSB is included in the recommendations.
Checking domains of the Cloud Security Benchmark
The Microsoft Cloud Security Benchmark checks your overall security and gives you recommendations about the following domains:
- Network security (NS)
- Identity Management (IM)
- Privileged Access (PA)
- Data Protection (DP)
- Asset Management (AM)
- Logging and Threat Detection (LT)
- Incident Response (IR)
- Posture and Vulnerability Management (PV)
- Endpoint Security (ES)
- Backup and Recovery (BR)
- DevOps Security (DS)
- Governance and Strategy (GS)
The recommendations look like the list below:
- AM-1: Track asset inventory and their risks
- AM-2: Use only approved services
- AM-3: Ensure security of asset lifecycle management
- AM-4: Limit access to asset management
- AM-5: Use only approved applications in virtual machine
The tool gives you overall recommendations which have previously compromised environments and are based on best practices to help you to secure you complete IT posture at all aspects. The aim is to secure all your systems, not just one.
For more information about this very interesting benchmark, check out this page: https://learn.microsoft.com/en-us/security/benchmark/azure/introduction
End of the page 🎉
You have reached the end of the page. You can navigate through other blog posts as well, share this post on X, LinkedIn and Reddit or return to the blog posts collection page. Thank you for visiting this post.
If you think something is wrong with this post or you want to know more, you can send me a message to one of my social profiles at: https://justinverstijnen.nl/about/
If you find this page and blog very useful and you want to leave a donation, you can use the button below to buy me a beer. Hosting and maintaining a website takes a lot of time and money. Thank you in advance and cheers :)
The terms and conditions apply to this post.
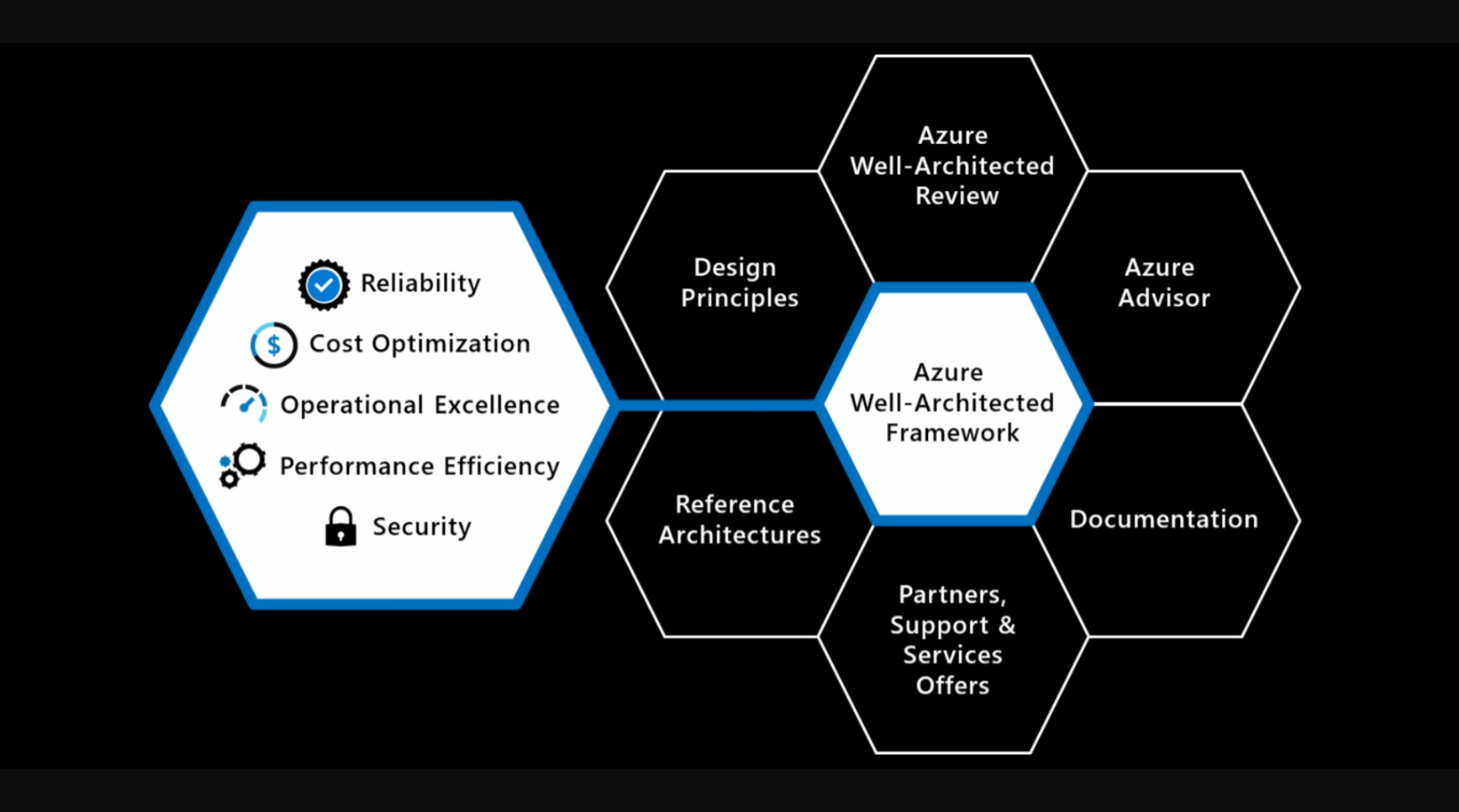
Introduction to the Azure Well-Architected Framework
The 5 pillars of the Well-Architected Framework are:
| Pillar | Target |
| Reliability | The ability to recover a system and/or contine to work |
| Security | Secure the environment in all spots |
| Cost Optimization | Maximize the value when minimizing the costs |
| Operational Excellence | The processes that keep a system running |
| Performance Efficiency | The ability to adapt to changes |
Like it is shown in the image up here is that the Well-Architected Framework is the heart of all Cloud processes. Without this well done, all other processes can fail.
Review your Azure design
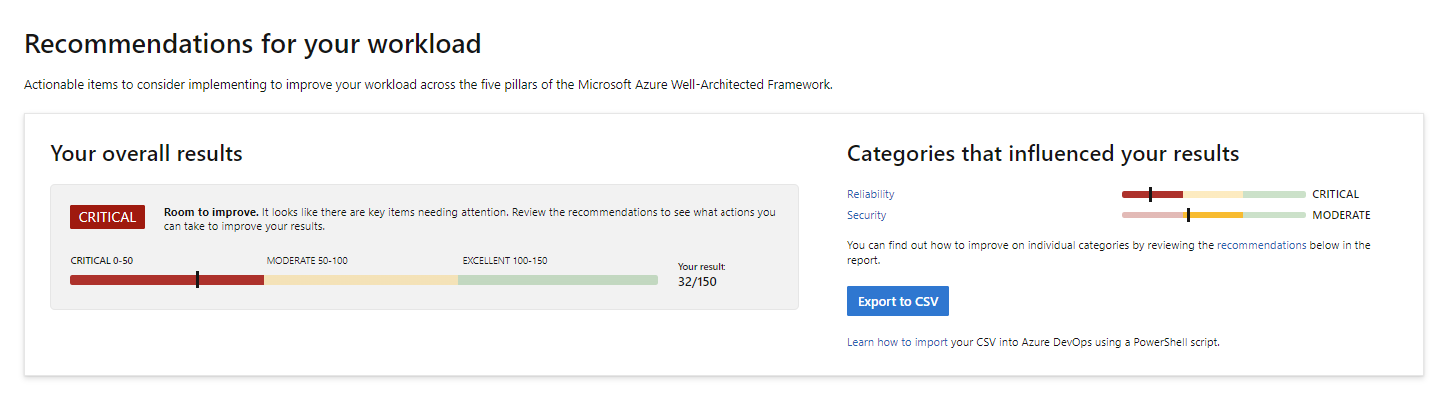
Microsoft has a tool available to test your architecting skills ath the following page: https://learn.microsoft.com/en-us/assessments/azure-architecture-review/
With this tool you can link your existing environment/subscription or answer questions about your environment and cloud goal. The tool will give feedback on what to improve and how.
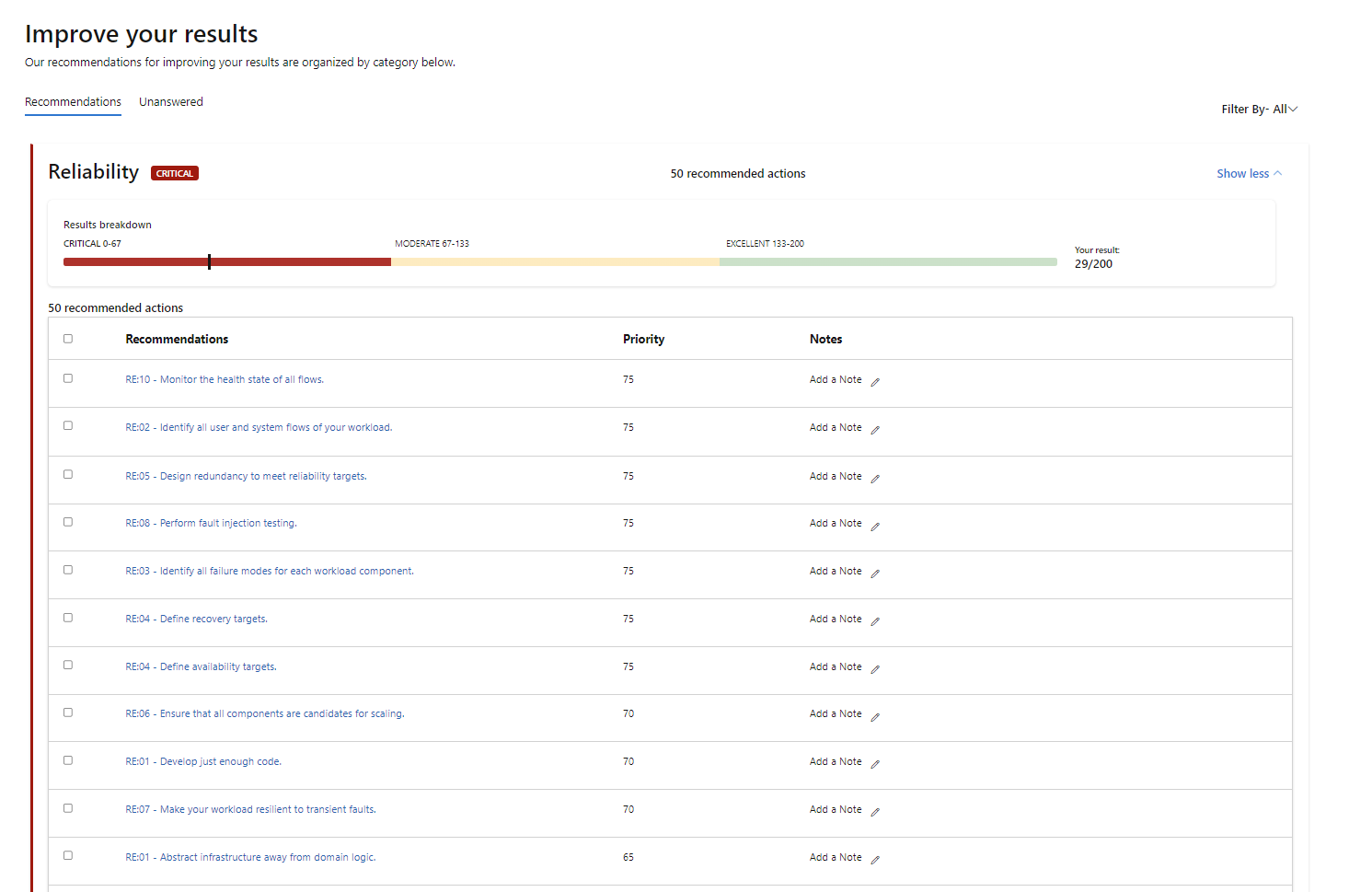
I filled in the tool with some answers and my result was this:
I only filled in the pillars Reliability and Security and filled it in as bad as possible to get as much as advices to improve. This looks like this:
End of the page 🎉
You have reached the end of the page. You can navigate through other blog posts as well, share this post on X, LinkedIn and Reddit or return to the blog posts collection page. Thank you for visiting this post.
If you think something is wrong with this post or you want to know more, you can send me a message to one of my social profiles at: https://justinverstijnen.nl/about/
If you find this page and blog very useful and you want to leave a donation, you can use the button below to buy me a beer. Hosting and maintaining a website takes a lot of time and money. Thank you in advance and cheers :)
The terms and conditions apply to this post.
Cloud Adoption Framework Introduction (CAF)
More and more organizations are moving to the cloud. In order to do this succesful, we can use the Cloud Adoption Framework which is described by Microsoft.
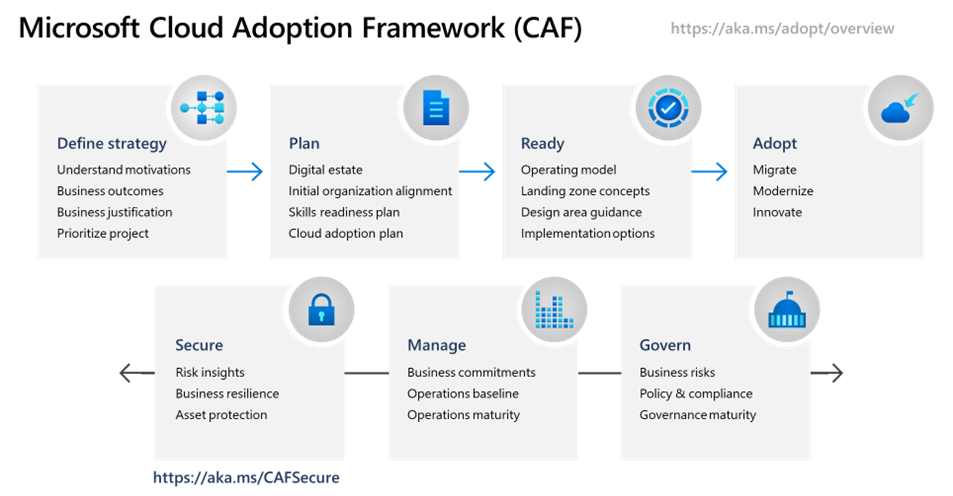
The framework is a succesful order of processes and guidelines which companys can use to increase the success of adopting the cloud. The framework is described in the diagram below:
The CAF has the following steps:
- Strategy: Define the project, define what you want to achieve and define the business outcomes.
- Plan: Plan your migration, determine the plans and make sure the environment readiness is at a good level.
- Ready (and migrate): Prepare your new cloud environment for planned changes and migrate your workloads to the cloud.
- Optimize: After migrating to the cloud, optimize your environment by using the beste solutions possible and innovate at this level.
- Secure: Improve the security of your workloads and plan your perodical security checks.
- Manage: Manage operations for cloud and hybrid solutions.
- Govern: Govern your environment and its workloads.
Intention of use
- Increase the chance of your cloud success
- Gives you a best practice of how to perform the migration by proven methodology
- Ensures you don’t miss a crucial step
Intended users/audience
- IT Decision makers
- Company Management Teams
- Companies who want to profit from cloud solutions
- Companies that are planning to migrate to the cloud
- Technicians and project managers for planning the migration
For more information, check out this page: https://learn.microsoft.com/en-us/azure/cloud-adoption-framework/scenarios/
Summary
This framework (CAF) can be very useful if your organization decides to migrate to the cloud. It contains a variety of steps and processes from earlier migrations done by companies and their faults.
End of the page 🎉
You have reached the end of the page. You can navigate through other blog posts as well, share this post on X, LinkedIn and Reddit or return to the blog posts collection page. Thank you for visiting this post.
If you think something is wrong with this post or you want to know more, you can send me a message to one of my social profiles at: https://justinverstijnen.nl/about/
If you find this page and blog very useful and you want to leave a donation, you can use the button below to buy me a beer. Hosting and maintaining a website takes a lot of time and money. Thank you in advance and cheers :)
The terms and conditions apply to this post.
AI-900 My learning journey
What is AI and what does Azure offer?
AI stands for Artificial Intelligence. It is a term for software that can make predictions, calculations, and estimates. It can act “smart” in a way that looks like human thinking.
Machine Learning (ML) is a type of AI. With ML, the system learns from the input data. More good data often means better results as the service has more data to base its decisions on.
Azure offers AI services across different areas, like:
- learning from data (Machine Learning)
- understanding images (Computer Vision)
- working with text and speech (NLP)
- searching and finding knowledge in large data (Knowledge Mining)
If you want a full study guide, you can start here:
- YouTube study guide: https://www.youtube.com/watch?v=bTkUTkXrqOQ
- PDF syllabus / study guide: https://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE4wGpB
1: Machine Learning
Machine Learning means that software learns from the data it receives. In many AI solutions, ML is seen as the “foundation”.
A typical goal of machine learning is:
- train a model with data
- then let the model make predictions or make choices
Example 1: Recognize apples
If software sees many apple images, it can learn what an apple looks like.
Then it can also estimate things like:
- “how rotten” an apple looks (for example: a percent)
In a real sorting process, you can use this to filter fruit (for example: mark B-quality) and automate decisions.
Example 2: Recognize a flower If you import many images of the same flower type, the software can recognize that flower across different photos and camera situations.
Azure offers functions to help with building ML solutions, like:
- Automated machine learning: Helps you create a model faster, even if you are not an ML expert.
- Azure Machine Learning designer: A visual (graphical) way to build ML solutions with less code (no-code style).
- Data and compute management: Cloud storage for data, so you can run experiments at larger scale.
- Pipelines: A way to define steps and automate tasks like model training and management.
We use two different outputs of Machine Learning:
- Regression: Predicts a continuous value (a number that can vary smoothly), like:
- sales per day
- quantity to buy
- revenue for a month/year
- Classification: Assigns a category (one of multiple choices), like:
- weather predictions
- a medical diagnosis
Azure Machine Learning Studio
Azure also has a specific tool for ML: https://ml.azure.com
In ML Studio, you create a workspace. A workspace is where you manage your ML setup, including compute options.
Your workspace can use 4 kinds of compute resources:
- Compute Instances: Developer workstations (for working with data and models)
- Compute Clusters: VM clusters for scale and processing when needed
- Inference Clusters: Used for running prediction services (when models are used to predict)
- Attached Compute: Links to existing Azure compute resources (for example VMs or Databricks)
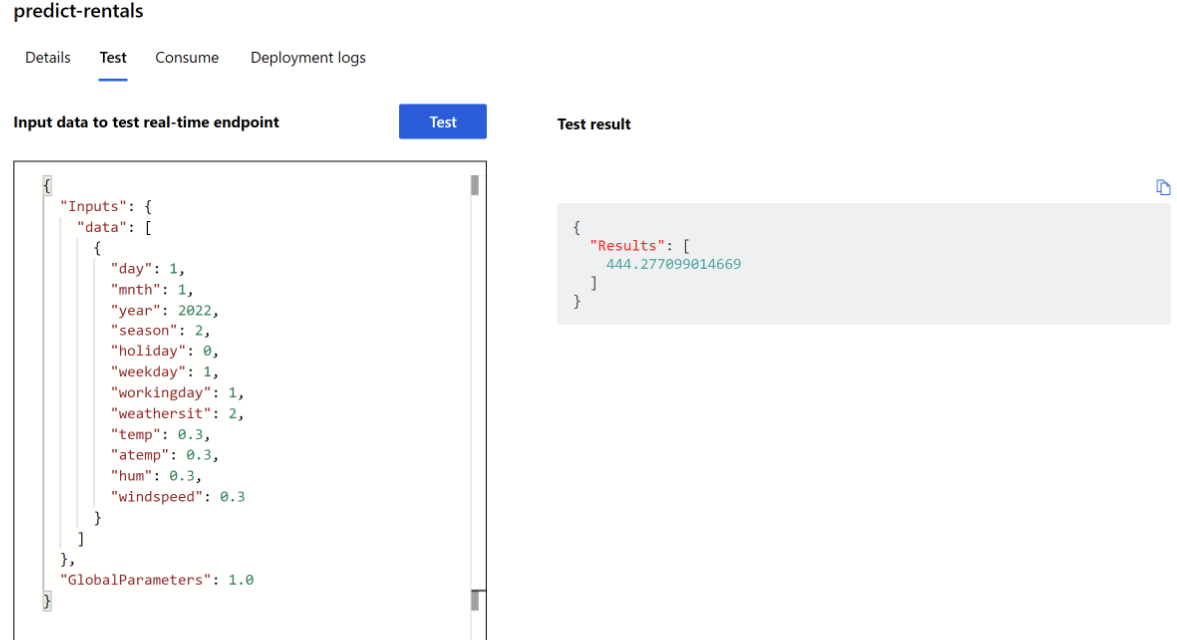
Practice example: Bike rental predictions
A bike rental company wants to predict how many bikes are available for a specific day.
They use historical data and input parameters such as:
- day, month, year
- season (spring/summer/autumn/winter)
- holiday (yes/no)
- weekday vs weekend
- workday (yes/no)
- weather (tropical/sunny/cloudy/rain)
- temperature
- humidity
- wind speed
With the data in a CSV file, Azure ML can predict how many bikes should be available on 1 January 2022. In the example, the prediction was 444 bikes, and the post notes that the result can change based on better predicted weather.
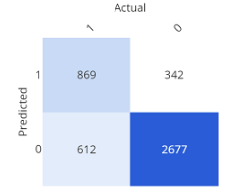
Confusion matrix (simple explanation)
A confusion matrix shows how often the expected and the real results match. It is one way to check model quality.
2: Guiding principles for implementing AI
Microsoft has guidance for building AI responsibly. Here are the main points, in simple terms:
- Fairness: AI should not discriminate. Example: in loan decisions, the system should not use gender, ethnicity, or religion to give someone an advantage or disadvantage
- Reliability and Safety: AI systems must work in a safe way and should be tested well. Example: if an AI model controls a vehicle or supports medical decisions, wrong results can cause serious harm
- Privacy and Security: Sensitive data must stay protected. Even after training, privacy and security should be monitored in production
- Inclusiveness: AI should help people and support better work for everyone, including people with different accessibility needs
- Transparency: Users should understand the goal, limits, and how the system works
- Accountability: People stay responsible for what AI does. Designers and developers should follow clear organization rules and frameworks so the solution is well-defined
3: Anomaly Detection
Anomaly Detection finds unusual patterns or “strange points” in data. This can help find issues like fraud or technical problems.
Example 1:
- In race sports: find a mechanical problem early, before it becomes critical.
- In production: detect faults in an automated production line at different times.
When anomalies are detected, you can trigger actions like:
- send a warning/alert
- run a script or automated fix process
Example 2: The post gives an example using an HVAC system (heating, ventilation, air conditioning).
AI can predict when temperature moves too high or too low, then trigger:
- extra cooling or heating
- alerts when a threshold is crossed
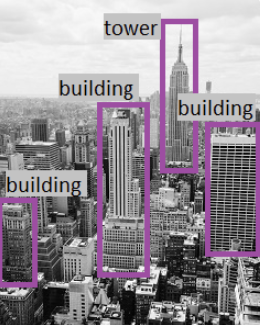
4: Computer Vision
Computer Vision is AI that can work with visual content (images). The post also mentions*Seeing AI, an app that can help blind or low-vision users by describing what is around them.
It can:
- describe an image in one sentence (max 10 words)
- read text (from a scan/photo)
- read money
- scan barcodes and explain the product
- recognize people
And it can also provide more image features:
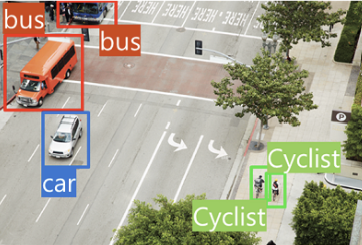
- Image classification: Find out what type of environment the image shows.
- Object detection: Detect different objects in an image.
- Semantic segmentation: Find which pixels belong to which object. Example is traffic monitoring where vehicles can be marked.
- Image analysis (tags): Describe an image using tags and confidence.The post says it can describe in up to 10 words by using the detected tags.
- Face detection, analysis, and recognition: Recognize faces and connect them to people. The post also states it can match known people and return an answer in about 2 seconds.
- Optical character recognition (OCR): Recognize characters in an image. The post uses Google Translate camera scan as an example.
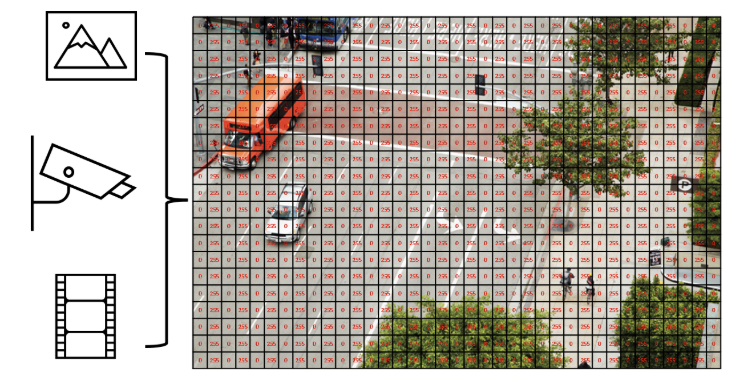
In AI, an image can be seen as numeric pixel values. These values can be used to train ML models that learn what the image content looks like.
Start using Computer Vision
To use Computer Vision, you need:
- a Computer Vision resource
- a Cognitive Services resource
Analyze an image (confidence)
Computer Vision can evaluate what objects are in an image and return a human-style description.
The results can include a confidence score, meaning how sure the service is about what it sees.
Example from the post (descriptions like):
- “A black and white photo of a city”
- “A black and white photo of a large city”
- “A large white building in a city”

It also creates tags (example tags in the post):
- skyscraper
- tower
- building
Then object detection can label what the objects are (example: “building”).
Face recognition
Computer Vision can:
- estimate age
- place a square/box around the face

Azure and Computer Vision
Azure can use the following services to create and implement into your own applications:
- Computer Vision
- Custom Vision
- Face
- Form Recognizer
5: Natural Language Processing (NLP)
Natural Language Processing (NLP) is AI that understands and recognizes written and spoken language. This can be used in different scenarios:
- read and understand text in documents and emails
- understand spoken language and answer
- translate spoken or written sentences
- understand user commands and actions
The post mentions a VR game named Starship Commander that uses NLP so players can talk and the game can respond. It uses AI for these scenarios:
- the game reacts to what you say
- the game responds in a personal way to characters
Azure services for NLP
- Language
- Translator
- Speech
- Azure Bot
6: Knowledge Mining
Knowledge mining is a definition for finding information inside large data sources, including data that is not well structured. The goal is to build a searchable knowledge store.
Azure Cognitive Search
Azure has a service named Cognitive Search that helps you:
- build indexes
- support search for internal use or a secured internet-facing search
Azure can process images in this manner and extract information from documents or images, so you can ask for specific stuff and Cognitive Search does the rest for you.Cognitive Search is a PaaS solution, where Microsoft manages the infrastructure.
It can support:
- full-text search and analysis
- text derived from images
- entity detection and key phrase detection (via text analysis)

Features of Azure Cognitive Search
- data from many sources
- full-text search and analysis
- AI-driven search requests
- multiple languages
- location-based search
- customizable user experience
7: Challenges and risks
AI is very helpful and powerful, but it needs responsible use. Microsoft lists these risks:
- Bias: can affect results.
- Example: a loan approval model may discriminate if trained on biased data.
- Errors can cause damage
- Example: if an autonomous vehicle fails, it can cause an accident.
- Data can be exposed
- Example: a medical bot trained on sensitive patient data needs strong protection.
- Solutions may not work for everyone
- Example: a smart home assistant may not provide audio output for visually disabled users.
- Users may need to trust a complex system
- Example: an AI tool gives investment advice, but where are the reasons coming from?
- Who is responsible for AI decisions?
- Example from the post: someone is wrongly convicted based on face recognition—who is accountable?
8: Machine Learning + Computer Vision Practice test
This part is a step-by-step guide of some of the features of Machine Learning and Computer Vision, which I did according to the course which was really fun to do. You can use the same idea to learn how training changes results.
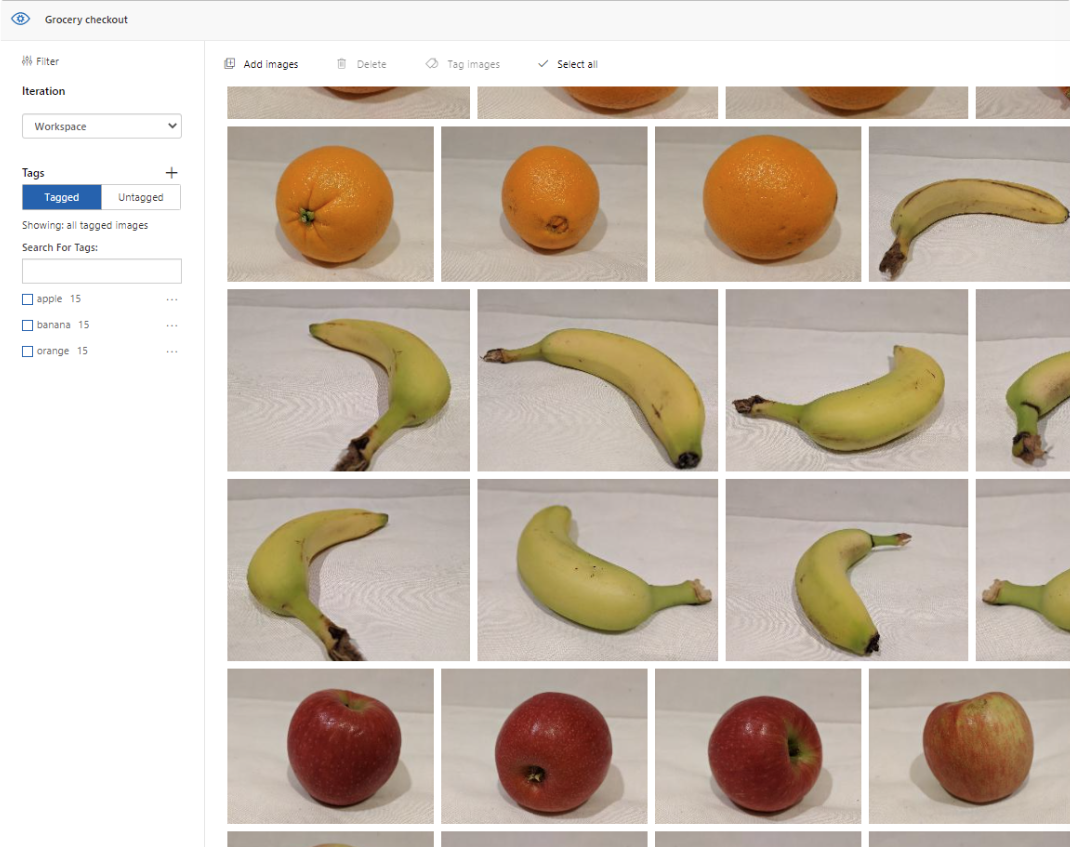
8.1: Preparing the training images
In the test environment, import 45 photos:
- 15 apple images
- 15 banana images
- 15 orange images
Source for the images: https://aka.ms/fruit-images
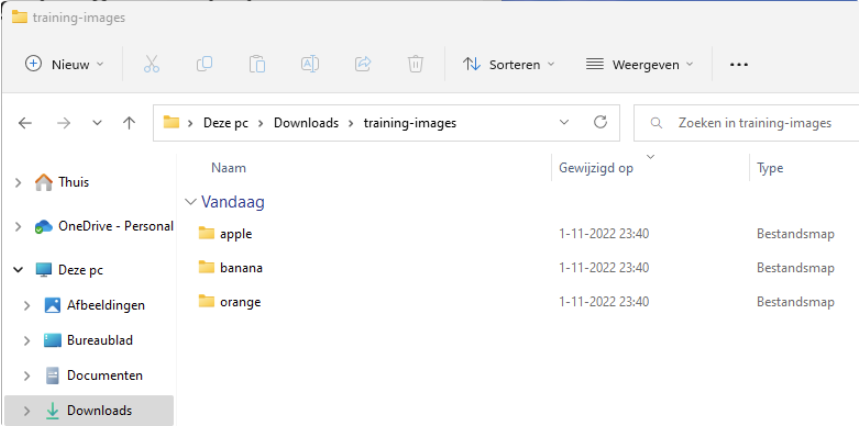
8.2: Importing into Cognitive Services and add tags
Import the photos into your Cognitive Services workspace.
When importing we add a tag so the system knows what each image is. After it learned what is an apple, what is a banana and what is an orange, the system uses these learned tags to judge new images.
8.3: Running a quick test
To test the system, we will quickly pick an image from google of an apple to see how sure the system is about other images which are slightly different than the images uploaded and trained with.
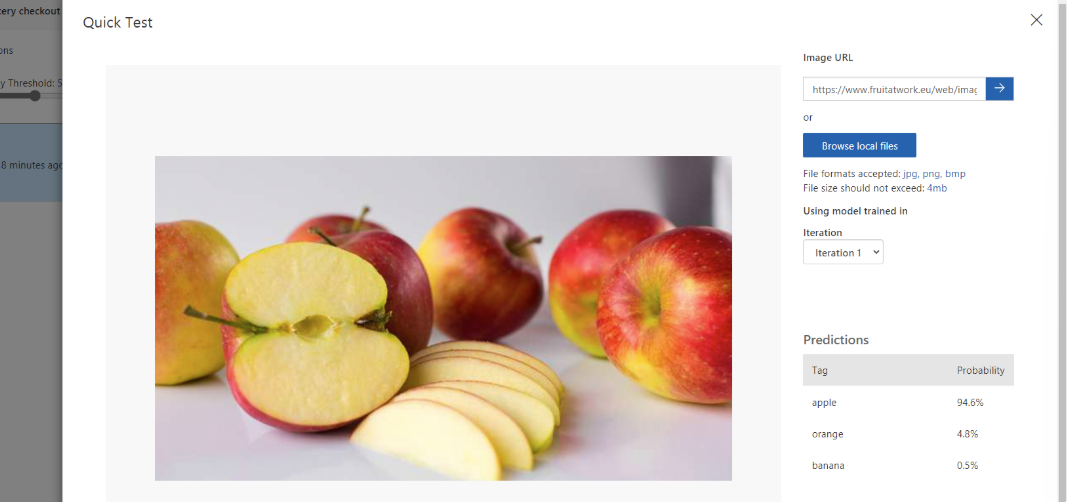
The system was 94.6% sure it was an apple, so this is already a very clever service.
8.4: Learning process
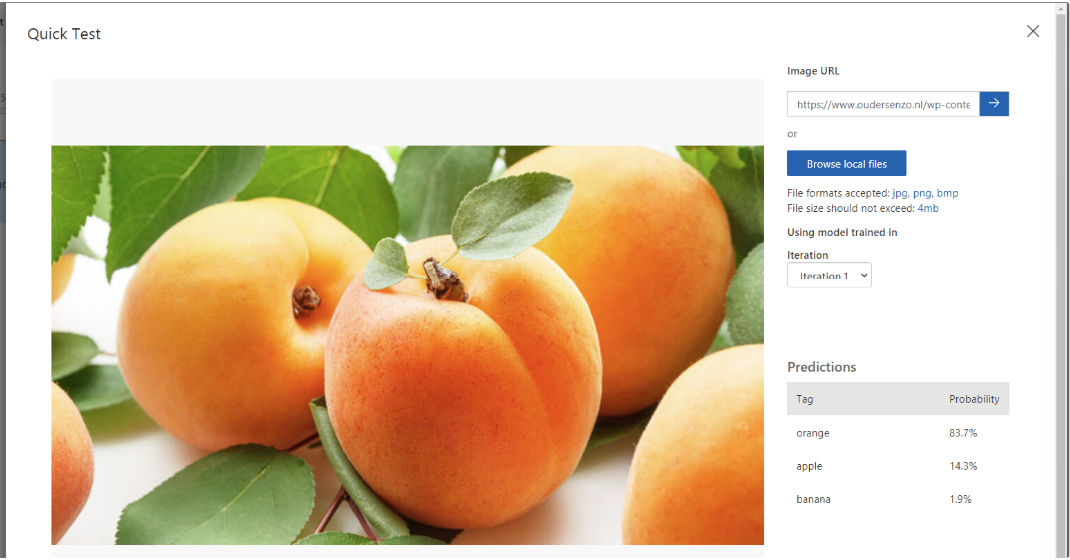
To teach the system something new, add apricot. This can give very fun results, as this can can be judged as:
- orange (color)
- apple (shape)
As a “0-measurement” test, I imported a picture of an apricot against the 3 known fruit types (apple, banana, orange). The post states the system predicted:
- 83.7% orange (mostly due to color)
- 14.3% apple (due to the same shape)
- 1,9% banana (doesnt find that much matching properties)
8.5: Uploading apricot images and train again
We will now upload 6 apricot photos, to train the service what a apricot is.
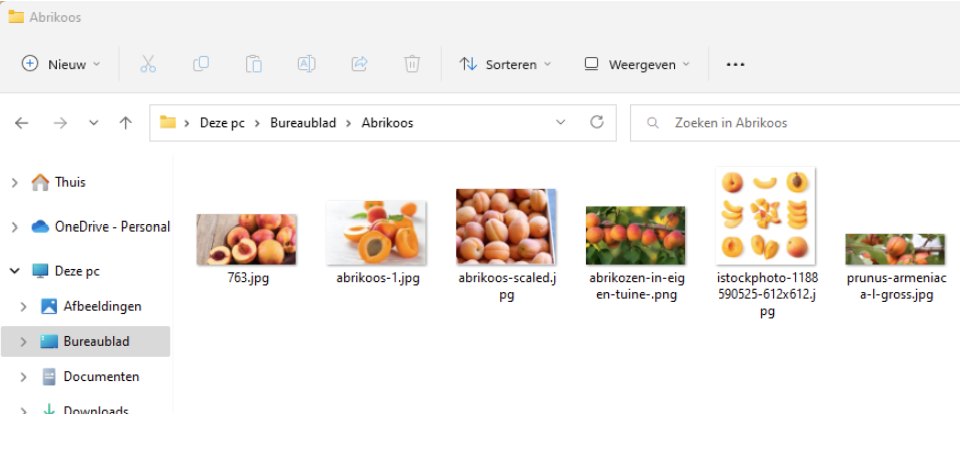
Add the tag:
- “apricot” (as the post says: “abrikoos”)
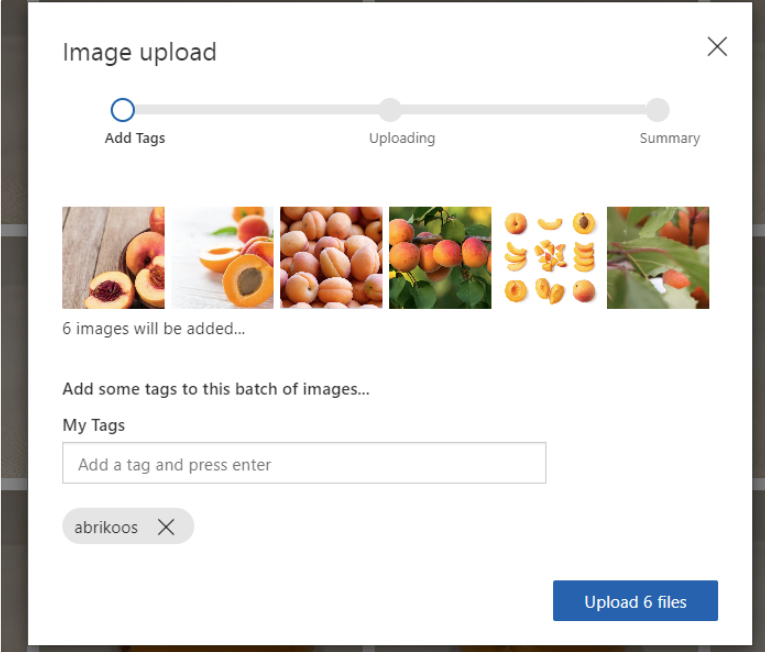
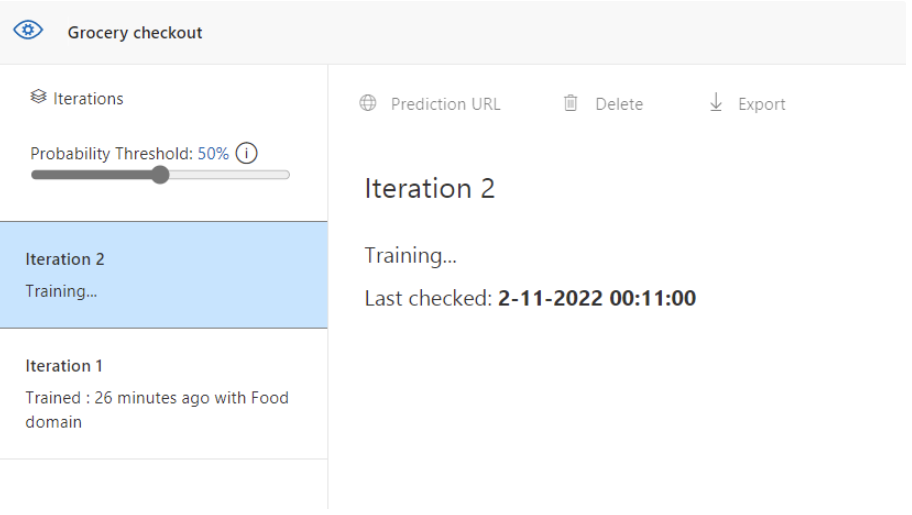
Then run training:
- Quick training (faster, but less compared to advanced training time/quality tradeoff mentioned in the post)
8.6: Test again with the same apricot image
After learning, test the same image again (from the 0-measurement). In the post, the result became:
- 98% apricot
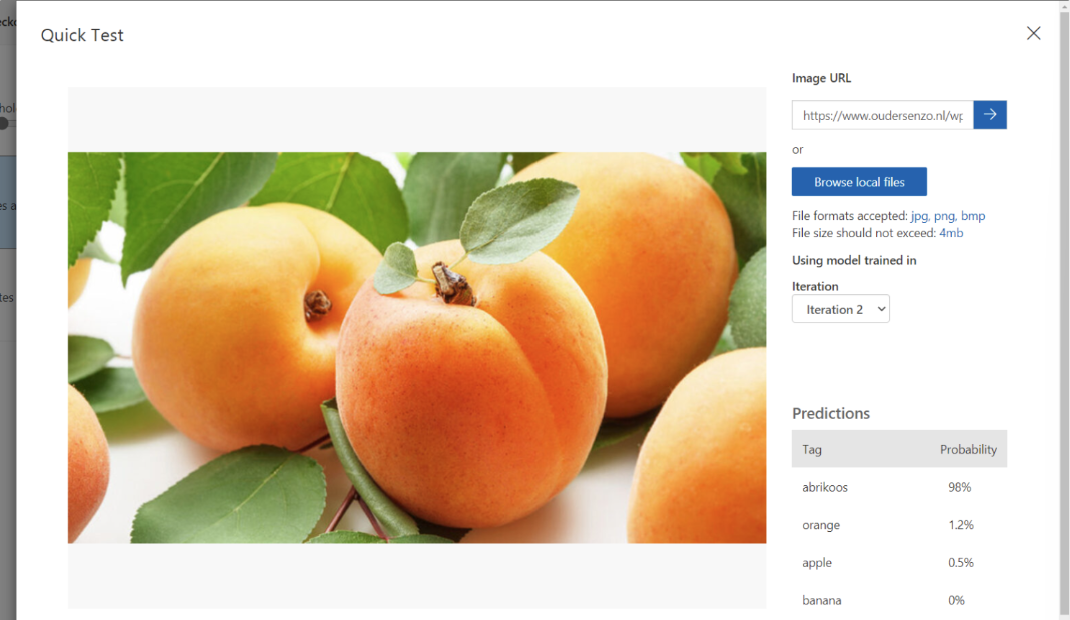
So, with only a few training/reference images, the system can learn a new category.
Summary
This post gave a simple overview of how Azure AI can be used:
- Machine Learning to learn from data and make predictions or categories
- Guiding principles for fairness, safety, privacy, transparency, and accountability
- Anomaly Detection to find unusual patterns in data
- Computer Vision to understand images (including confidence scores and image tagging)
- NLP to work with text and speech
- Knowledge Mining to build searchable knowledge using Cognitive Search
Thank you for reading this post and I hope it was helpful!
Sources
These sources helped me by writing and research for this post;
- https://www.youtube.com/watch?v=bTkUTkXrqOQ
- https://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE4wGpB
- https://ai.azure.com
- https://aka.ms/fruit-images
End of the page 🎉
You have reached the end of the page. You can navigate through other blog posts as well, share this post on X, LinkedIn and Reddit or return to the blog posts collection page. Thank you for visiting this post.
If you think something is wrong with this post or you want to know more, you can send me a message to one of my social profiles at: https://justinverstijnen.nl/about/
If you find this page and blog very useful and you want to leave a donation, you can use the button below to buy me a beer. Hosting and maintaining a website takes a lot of time and money. Thank you in advance and cheers :)
The terms and conditions apply to this post.